
OWASP TOP 10
OWASP Top 10 Application Security Risks – 2017
- Injection flaws, such as SQL, NoSQL, OS, and LDAP injection, occur when untrusted data is sent to an interpreter as part of a command or query. The attacker’s hostile data can trick the interpreter into executing unintended commands or accessing data without proper authorization.
- Application functions related to authentication and session management are often implemented incorrectly, allowing attackers to compromise passwords, keys, or session tokens, or to exploit other implementation flaws to assume other users’ identities temporarily or permanently.
A3:2017-Sensitive Data Exposure
- Many web applications and APIs do not properly protect sensitive data, such as financial, healthcare, and PII. Attackers may steal or modify such weakly protected data to conduct credit card fraud, identity theft, or other crimes. Sensitive data may be compromised without extra protection, such as encryption at rest or in transit, and requires special precautions when exchanged with the browser.
A4:2017-XML External Entities (XXE)
- Many older or poorly configured XML processors evaluate external entity references within XML documents. External entities can be used to disclose internal files using the file URI handler, internal file shares, internal port scanning, remote code execution, and denial of service attacks.
- Restrictions on what authenticated users are allowed to do are often not properly enforced. Attackers can exploit these flaws to access unauthorized functionality and/or data, such as access other users’ accounts, view sensitive files, modify other users’ data, change access rights, etc.
A6:2017-Security Misconfiguration
- Security misconfiguration is the most commonly seen issue. This is commonly a result of insecure default configurations, incomplete or ad hoc configurations, open cloud storage, misconfigured HTTP headers, and verbose error messages containing sensitive information. Not only must all operating systems, frameworks, libraries, and applications be securely configured, but they must be patched/upgraded in a timely fashion.
A7:2017-Cross-Site Scripting (XSS)
- XSS flaws occur whenever an application includes untrusted data in a new web page without proper validation or escaping, or updates an existing web page with user-supplied data using a browser API that can create HTML or JavaScript. XSS allows attackers to execute scripts in the victim’s browser which can hijack user sessions, deface web sites, or redirect the user to malicious sites.
A8:2017-Insecure Deserialization
- Insecure deserialization often leads to remote code execution. Even if deserialization flaws do not result in remote code execution, they can be used to perform attacks, including replay attacks, injection attacks, and privilege escalation attacks.
A9:2017-Using Components with Known Vulnerabilities
- Components, such as libraries, frameworks, and other software modules, run with the same privileges as the application. If a vulnerable component is exploited, such an attack can facilitate serious data loss or server takeover. Applications and APIs using components with known vulnerabilities may undermine application defenses and enable various attacks and impacts.
A10:2017-Insufficient Logging&Monitoring
- Insufficient logging and monitoring, coupled with missing or ineffective integration with incident response, allows attackers to further attack systems, maintain persistence, pivot to more systems, and tamper, extract, or destroy data. Most breach studies show time to detect a breach is over 200 days, typically detected by external parties rather than internal processes or monitoring.
Metasploit辅助模块
扫描模块
load wmap 加载模块 help 帮助 wmap_sites -a http://202.112.50.74 添加网站 wmap_sites -l wmap_targets -t http//202.112.50.74 添加网站作为目标网站 wmap_run -t 查看那些模块在扫描种会给用到 wmap_run -e 启动 vulns 显示扫描结果
渗透模块
Web应用扫描款式较多,估计目前已经上百种,
选择自己常用或觉得好的,下面只列书中提到的
Arachni Grabber-Scan Wapiti Zed Attack Proxy Skipfish W3AF Sandcat Free Edition Paros Burp suit Free WATOBO
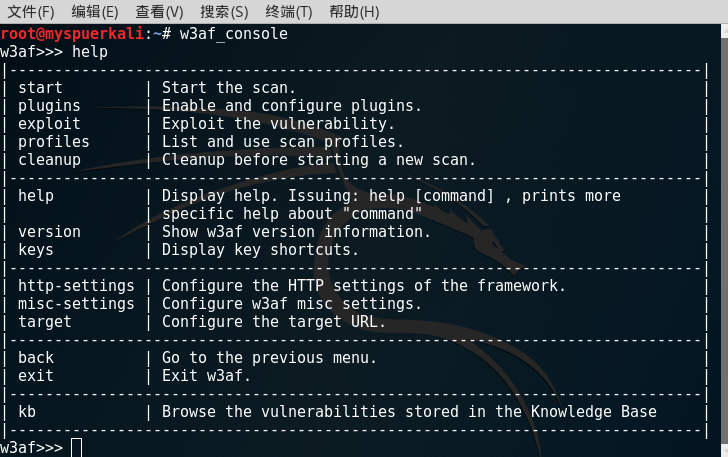
扫描神器W3AF(Web Application Attack adn Framework)
w3af_console 命令行
help 帮助
漏洞扫描配置
w3af>>> plugins //进入插件模块 w3af/plugins>>> list discovery //列出所有用于发现的插件 w3af/plugins>>> discovery findBackdoor phpinfo webSpider //启用findBackdoor phpinfo webSpider这三个插件 w3af/plugins>>> list audit //列出所有用于漏洞的插件 w3af/plugins>>> audit blindSqli fileUpload osCommanding sqli xss //启用blindSqli fileUpload osCommanding sqli xss这五个插件 w3af/plugins>>> back //返回主模块 w3af>>> target //进入配置目标的模块 w3af/config:target>>> set target http://192.168.244.132/ //把目标设置为http://192.168.244.132/ w3af/config:target>>> back //返回主模块 w3af>>> start //漏洞扫描
漏洞利用配置
w3af>>> exploit //进入漏洞利用模块 w3af/exploit>>> list exploit //列出所有用于漏洞利用的插件 w3af/exploit>>> exploit sqlmap //使用sqlmap进行SQL注入漏洞的测试
漏洞利用
w3af/exploit>>> interact 0 //interact + shell object就可以利用了 w3af/exploit/sqlmap-0>>> dbs //sqlmap的一个交互式模块
wXf工具
因Kali Linux没有集成,工具是2010年的,长久没有更新。
仿造Metasploit,所以没有深入了解了
SQL注入,XSS,
初步改写Metasploit exploit攻击模块
文件包含和文件上传
本地包含—可查看主机上面的任意文件
远程包含—直接可远程执行WebShell,需allow_url_include选项开启